Launching auxcord.org - Let friends queue their music at your party
- You host a party
- You play a playlist
- Friend wishes song
- You give them your phone
- Your playlist stops
- They change volume
- Song over
- Your playlist gone
- Party dead
Auxcord.org is a simple, free service:
Simply connect your Sonos and Spotify account, and manage your party in one spot:
- Never replace the currently playing song: always queue
- Your guests can use any phone to add songs
- Your guests don't need any account or login
- Disable the speaker's hardware buttons, so you control the volume and playlist
- Share a link or QR code ahead of time, so guests can pre-queue
- Prevent the same song from being played multiple times
- No need to hand over your phone, or have your friends spell the title of the song
Currently, Auxcord works with Sonos & Spotify. The project is free to use, however not yet open source. Depending on demand, I might open source the repo on GitHub.
It’s like a Jukebox, but for your Sonos & Spotify setup.
Open Auxcord.org here to start using it for your next party.
Tags: spotify, sonos, music, party | Edit on GitHub
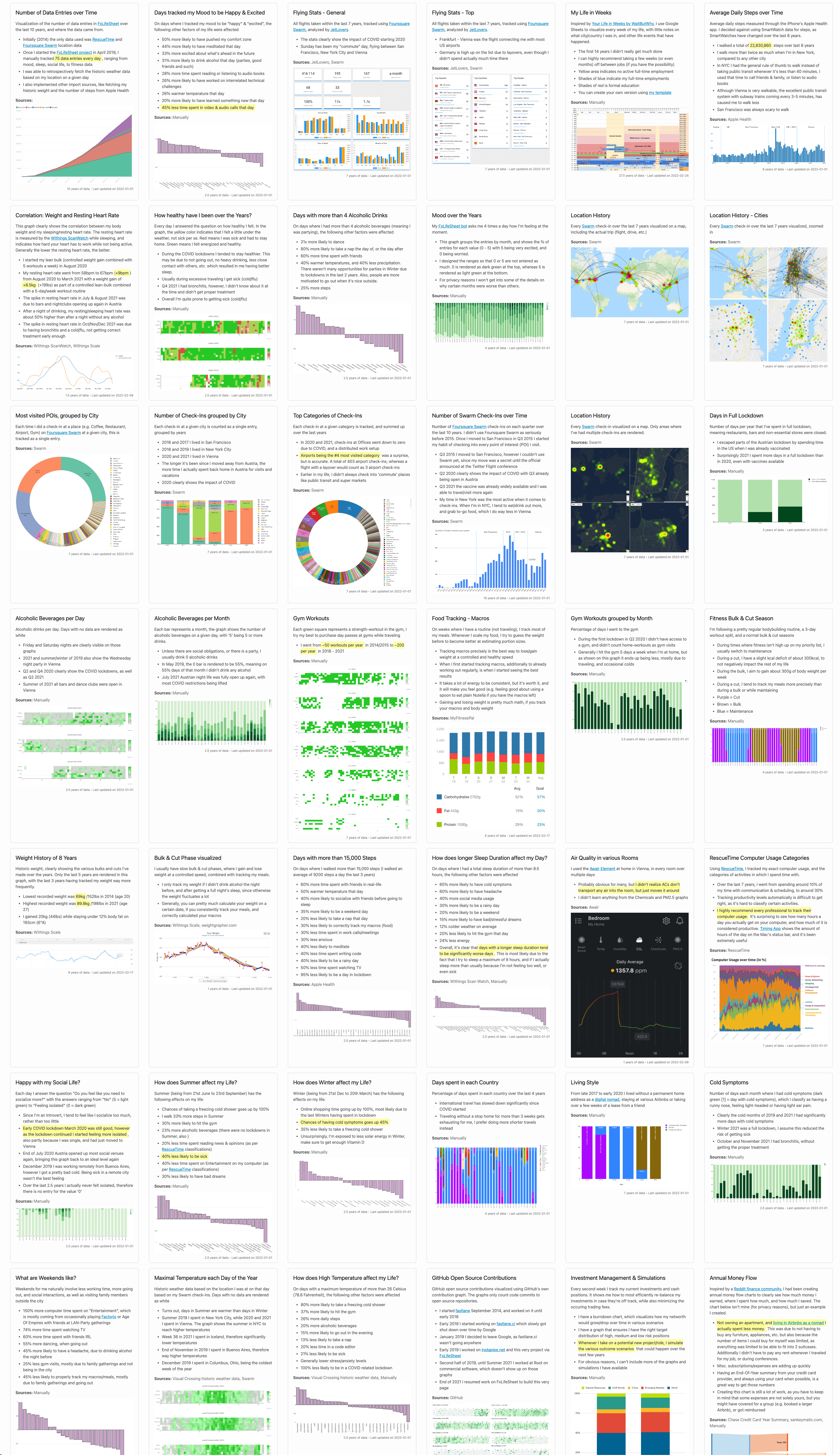
How I put my whole life into a single database
Back in 2019, I started collecting all kinds of metrics about my life. Every single day for the last 2.5 years I tracked over 100 different data types - ranging from fitness & nutrition to social life, computer usage and weather.
The goal of this project was to answer questions about my life, like
- How does living in different cities affect other factors like fitness, productivity and happiness?
- How does sleep affect my day, my fitness level, and happiness?
- How does the weather, and the different seasons affect my life?
- Are there any trends over the last few years?
- How does computer time, work and hours in meetings affect my personal life?
Since the start of this project, I collected a total of more than 380,000 data points.
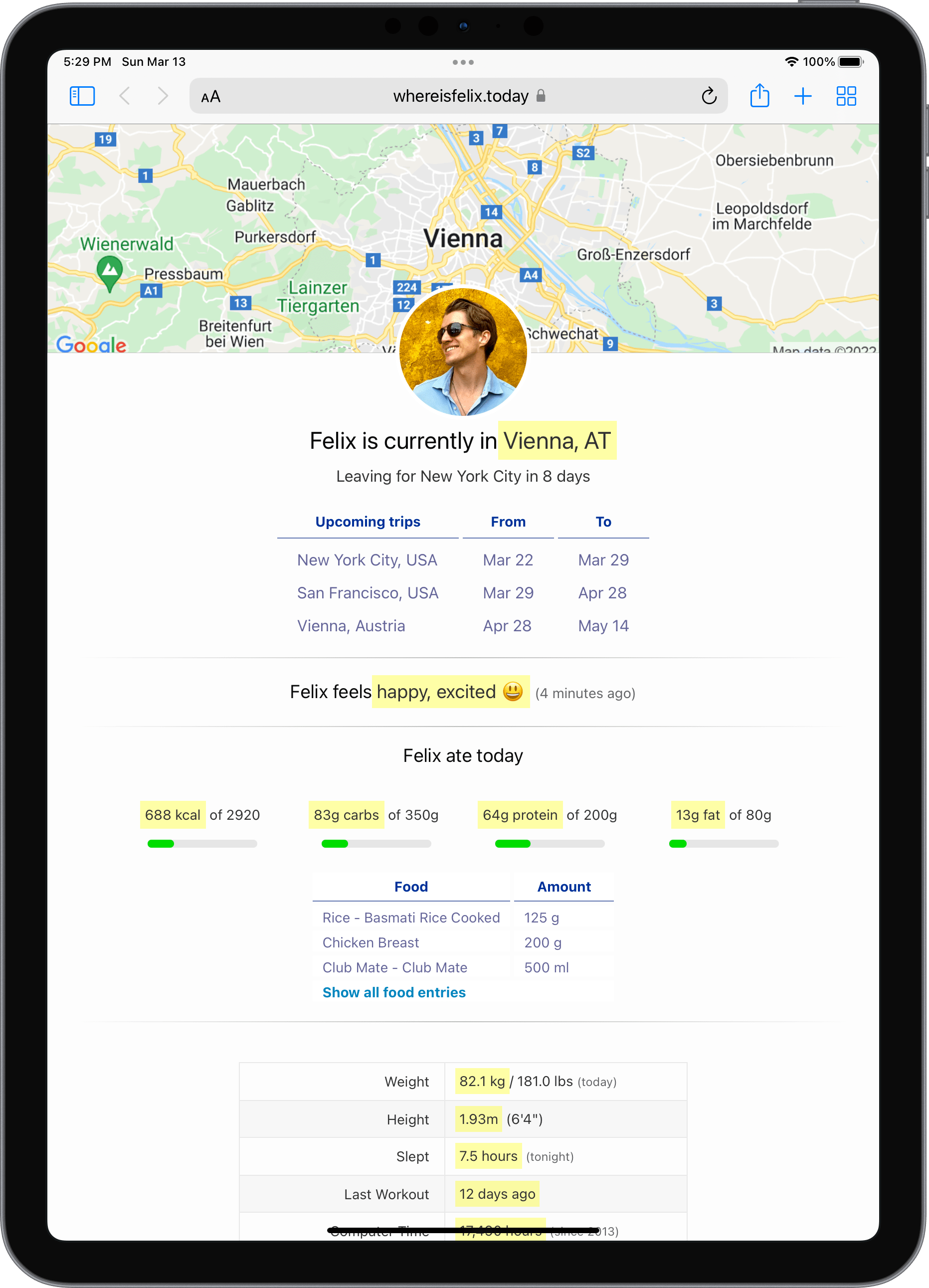
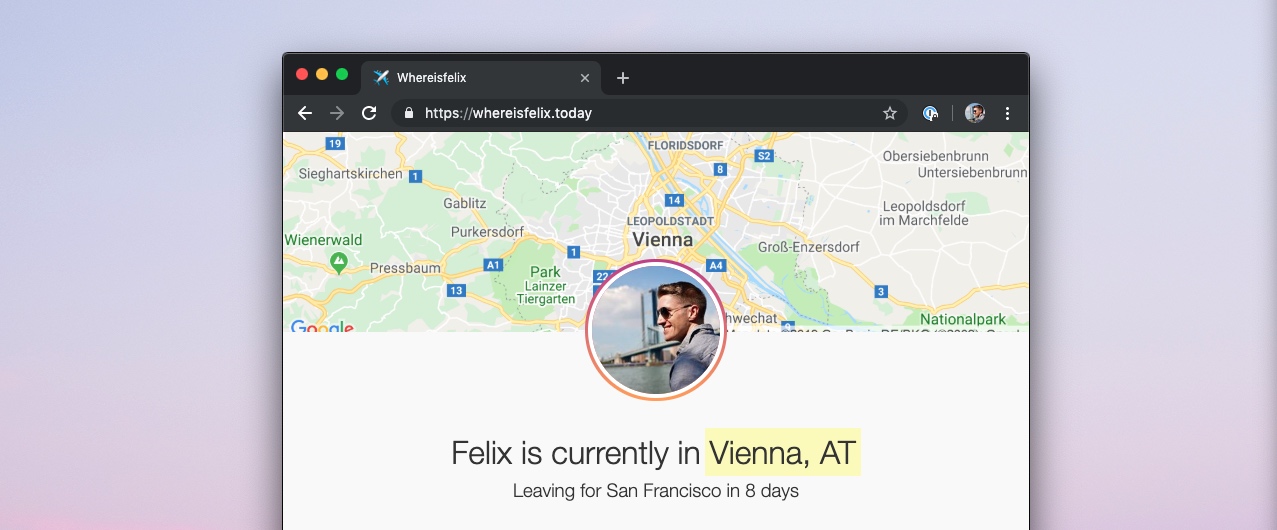
Naturally after I started collecting this data, I wanted to visualize what I was learning, so I created howisFelix.today. Initially, the domain whereisFelix.today (now renamed to howisFelix.today) started as a joke to respond to friends asking when I’d be back in NYC or San Francisco. Rather than send them my schedule, I’d point them to this domain. However, now it’s more than my location: it’s all of me.
Rules I setup for the project
- Use a single database, owned and hosted by me, with all the data I’ve collected over the years
- Be able to easily add and remove questions on the fly, as I learn what’s beneficial to track
- Full control of how the data is visualized
- Works well for frequent flyers with mixed time zones
- 100% fully open source, MIT licensed and self-hosted
I selected 42 graphs to show publicly on howisFelix.today
Check out howisFelix.today to see all graphs and data I’ve created with this project, as well as details about how you can use this project for yourself. You can check out the full source code on KrauseFx/FxLifeSheet.
Tags: quantified-self | Edit on GitHub
iOS Privacy: Detect when an iOS user hits the Safari share button
Summary
Whenever you hit the “Share” button in iOS Safari, a request gets sent to fetch an iOS home screen app icon, which can be used to track the event.
Safari
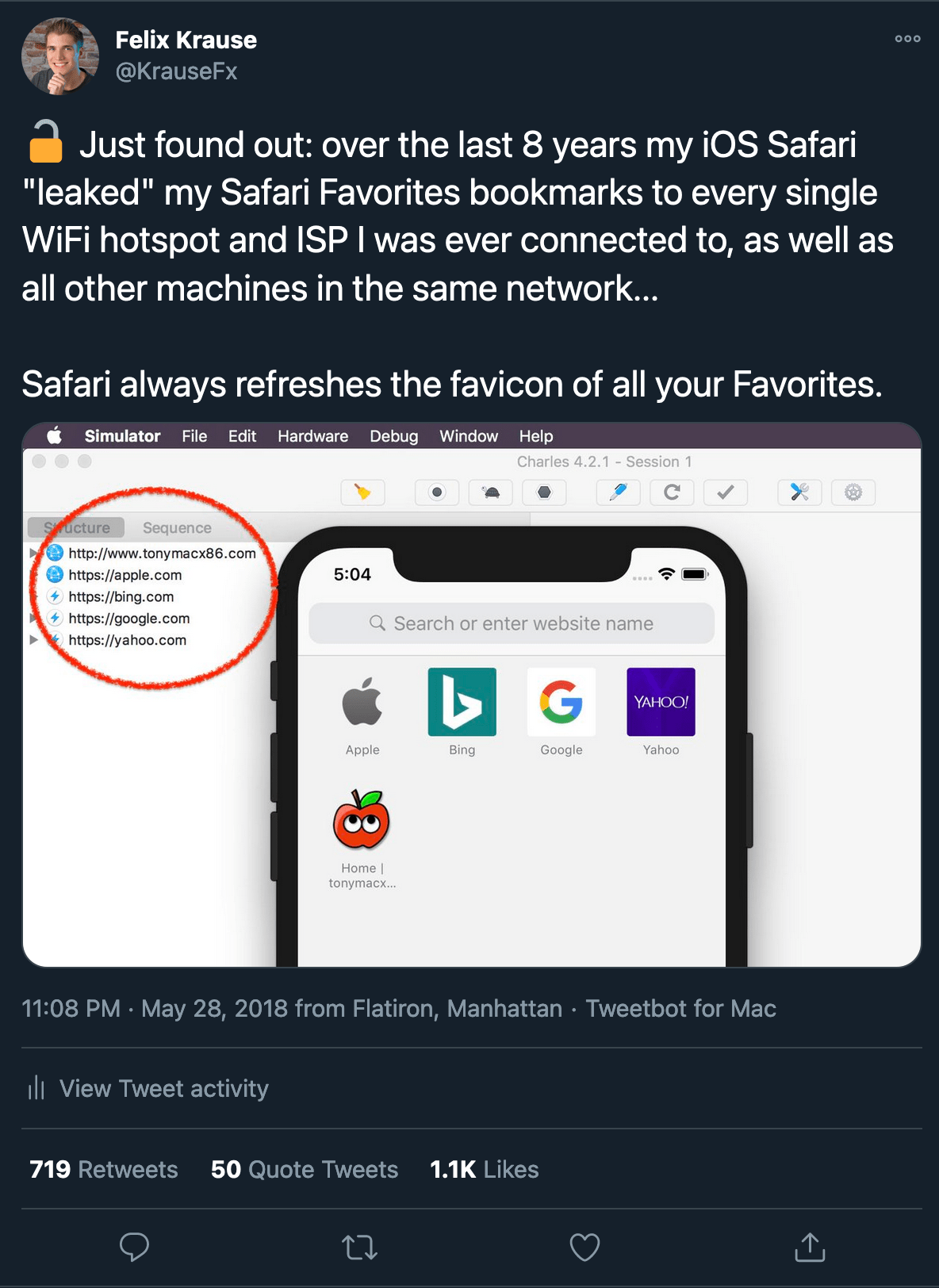
Safari is a great browser, that puts user privacy first. However it could still be better. In 2018 I published some details on how iOS Safari has leaked my bookmark for the last 8 years to all ISPs, WiFis and VPNs I was ever connected to. This was especially interesting, as I haven’t used the bookmarks feature in forever, and those bookmarks pointed to OSx86 guides from when I couldn’t afford a real Mac:
Context
Recently when working on some backend code, I noticed some extra requests that were received by my web server:
![]()
Those requests (e.g. apple-touch-icon-precomposed.png) are being sent to get the app icon that are used when the user adds your website onto their home screen. All of this makes sense, however they are sent immediately when the user hits the share button, instead of later in the flow when the user actually chooses the Add to Home Screen option.
The proof of concept is available on GitHub at KrauseFx/privacy-share-button, it’s a very basic Sinatra + plain HTML/JS website. The server keeps track of the apple-touch-icon requests per IP address, and the client simply polls to get the status of it. However there is no reason to render the status on the frontend in the first place.
Why does it matter?
While this isn’t a big privacy problem, it still is an issue that could easily be prevented by Apple. New social media apps like TikTok make use of sharing behaviors on their platform, growth marketers care a lot about all kinds of data, and this getting some extra context on if certain content is being shared outside their platform is most likely very much in their interest.
This allows the website operator to also guess with good accuracy which content the user hit the share button for, by looking up the most recent page they opened up.
Similar projects I’ve worked on
I published more posts on how to access the camera, the user’s location data, their Mac screen and their iCloud password, check out krausefx.com/privacy for more.
Tags: ios, privacy, safari | Edit on GitHub
instapipe.net - Distribute your Instagram stories
Background
You want to share experiences as they are happening in your life. Instagram Stories is a great way to do so, thanks to cross-posting to Facebook, Messenger and Instagram itself, allowing most people to view your stories.
However just like Snapchat, the platforms try to lock you in, with the content you create. Many of my family members and close friends don’t use FB/IG daily, but still wanted to stay up to date on what I’m up to.
Due to lack of an official API, and any kinds of integrations, the only way to access your stories is through the inofficial API the Instagram mobile- and web client use.
Solution
A simple web service that automatically downloads and publishes your stories on various platforms. It’s open source and fully self hosted, check it out on GitHub.
Embed into websites
Showing what you’re up to on the websites you operate is an easy way to make your online presence more personal.
- On howisFelix.today?
- Integrated into krausefx.com (desktop only)
- Plain live demo
Features
- Design similar to instagram.com web
- Arrow keys to go back and forth between stories
- Support for photos and videos
- Support for desktop and mobile browsers
- Dismiss stories using ESC key, and clicking the dimmed area
- Pre-loading of the next story for instant rendering
- Basic features like rendering of the progress bar, the relative time stamp, as well as linking to your profile
- Zero dependencies, plain JavaScript, CSS and HTML in a single file
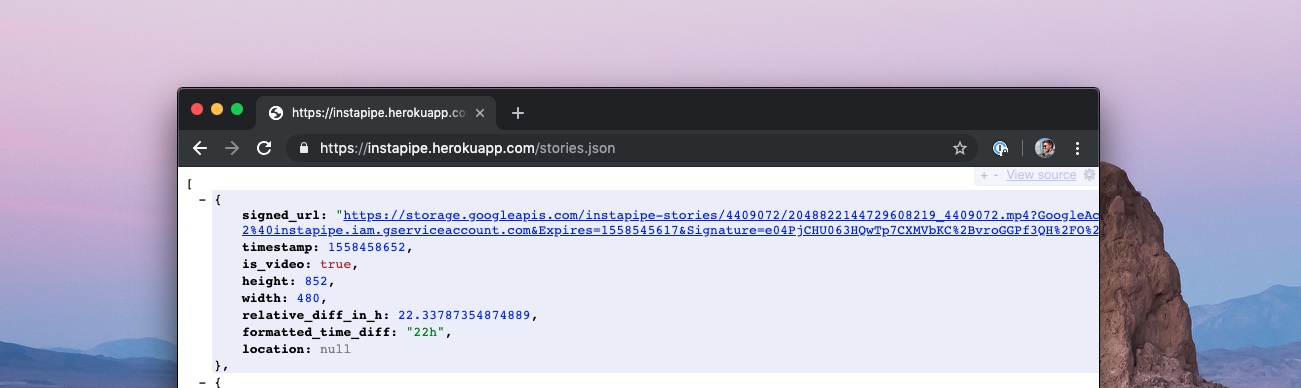
Provide a JSON API
Of course it also provides you with a JSON API, that can be used to integrate your Instagram stories into any app or service. The API includes all relevant data, including the raw image, location and the exact resolution of the media assets.
Telegram group
Many of my friends don’t want to check Instagram every day, but still want to stay up to date with what I’m up to. Since they all use Telegram already, I set up a channel that automatically shows the stories I post.
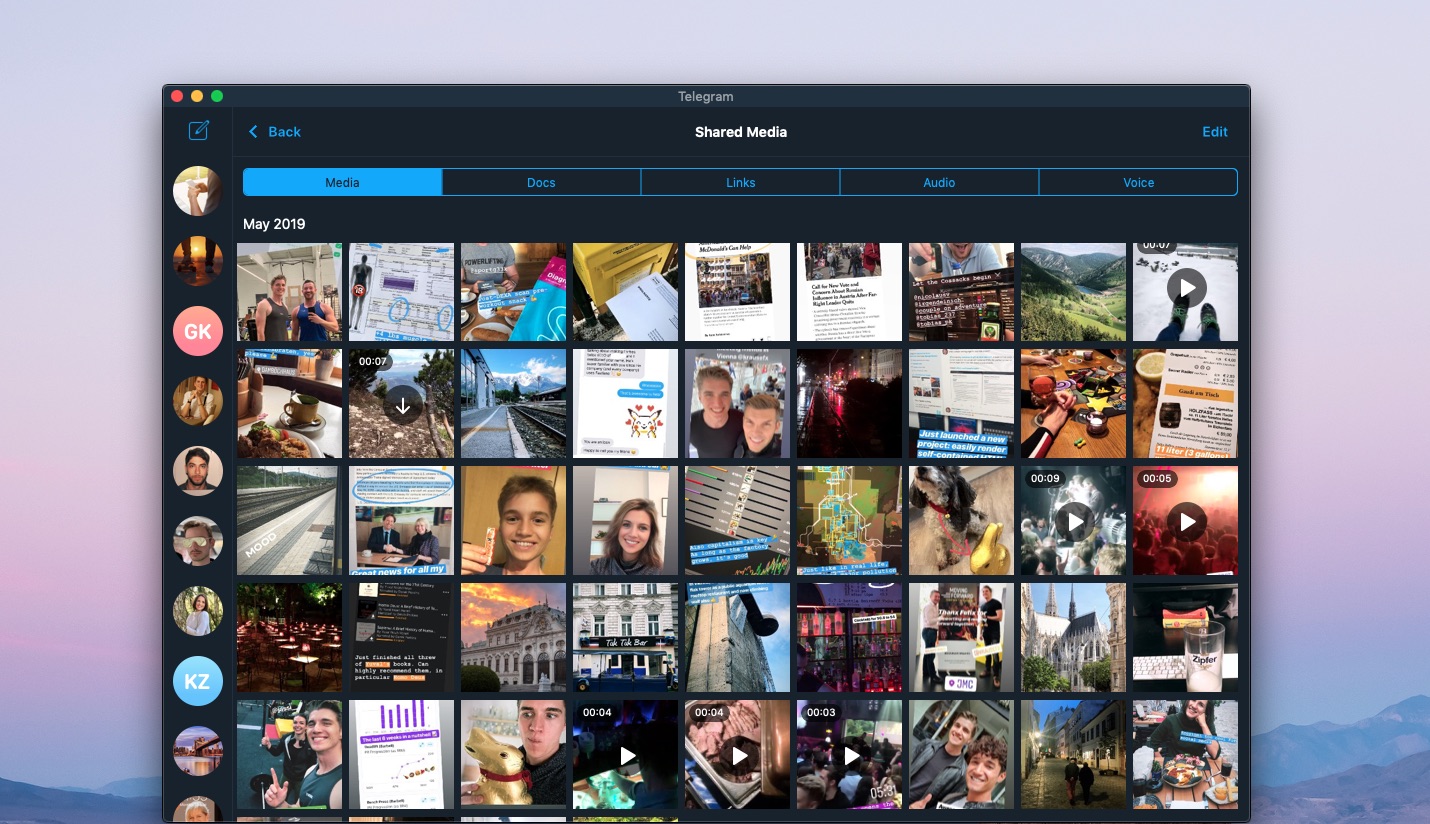
A Telegram group containing all my latest stories. In particular nice to get an overview over all your most recent stories.
How it works
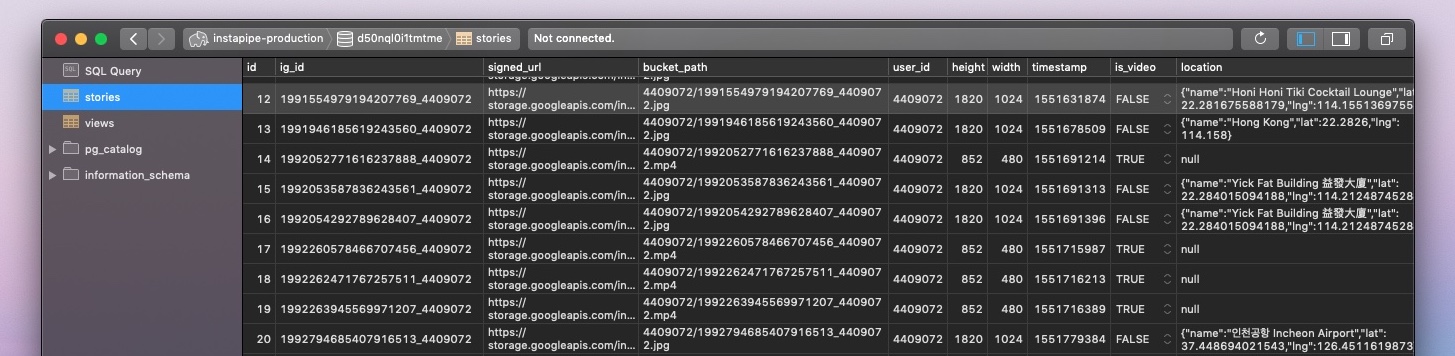
Instapipe is a simple server, that periodically fetches your most recent Instagram stories. As soon as a new story is available, it will
- Download the highest resolution photo/video and store it on your personal Google Cloud Bucket
- Store the associated metadata in a database you own, the data includes
- 24 hours signed URL to the full-resolution photo/video of your Google Cloud Storage
- The full path of the resource referencing your Google Cloud bucket
- The user ID who published the asset
- The height and width of the photo/video
- The exact time stamp of publishing
- An
is_videoflag - The location (if a location tag is attached)
- Location Name (e.g.
Das Gym) latandlngcoordinates
- Location Name (e.g.
- Post the new story into a Telegram group
Open instapipe.net
Tags: open-source, instagram, telegram | Edit on GitHub